About Us
Our roots in IP
The Ehrlich Group offers new clients access to some of the finest legal and technical minds in the industry, with more than 160 employees who have worked as jurists, patent attorneys and technical advisors. Our firm can claim renowned experts in all areas of Intellectual Property, including Patents, Copyrights, Trademarks, Designs, Trade Secrets Plant Breeder’s Rights, Anti-Counterfeiting, Open Source, and much more.
Our Technological Fields
Technological Fields

BioTech
BioTech has the potential to change the future of humanity.

Computing Technologies
When It Comes to Software Protection, The Combination of Technical and Legal Understanding Is Key.

HighTech
The Ehrlich Group Protected Thousands of ground breaking Technologies.

Chemistry & Pharma
IP is the engine of so many companies in the chemistry and pharmaceutical sectors and it must be protected.

Medical Devices
Patent protection in the complex and multidisciplinary medical devices market is a critical part of the strategy.

Physics
Applying principles of physics to day-to-day challenges is patentable.
Services
Our Services
Understandig Your Needs
Patents can provide powerful leverage for your business. Whether they cover the products, the machines or materials that make your products, or the processes you use, they are a valuable part of your start-up and business. They can stop other companies from using your technology to develop a rival, can generate revenue and also create strong relationships with companies that need your product or technology.
Your first step towards protecting your invention is to consider patents for intellectual property protection. While there are also other IP rights you should consider, like trade secrets, designs, and even copyrights, each with their own requirements and benefits, we help you to decide which is the best and most appropriate course of action to protect your IP.
Adding Value
Should patenting your invention be the right IP move, our IP experts are well equipped to make sure your invention is covered from every possible angle to maximize your company’s market opportunity. Once protected, we help you to build IP portfolios, where necessary, and tailor a strategy to your particular needs, covering every aspect of protecting computer-based and other inventions, including patent prosecution worldwide, patent enforcement and litigation, monetization and transactions of technology, and regulatory matters.
Here for You
With a large roster of start-ups, entrepreneurs, well-established corporates, government agencies and independent research institutions, Ehrlich Group’s team of experts are up-to-speed on all local and foreign IP legislation, and also includes foreign-licensed patent attorneys who can help with questions on foreign jurisdictions. On all types of patent litigation, clients have instant access to the Ehrlich Group’s hugely experienced litigators who have successfully resolved patent infringement and many other types of disputes for some of Israel’s most well-known businesses.
If you have any questions regarding your patent needs, feel free to contact us.
Understandig Your Needs
Designs – sometimes called industrial designs or a design patent – is an intellectual property right aimed at protecting the aesthetics of an industrial product. In fact, in many cases, a client will need to file both a utility patent to protect the functionality of its invention and a design patent to protect its aesthetics.
Protecting the way your product looks can often be integral to its value. A design patent allows you to protect this value. Our IP experts are well equipped to handle all aspects of protecting clients’ designs, tapping into our specialized knowledge and practical experience in the design registration process and an in-depth understanding of the broadest range of industries.
Adding Value
Having prepared and filed design registration applications in Israel, US and around the world, clients have at their disposal a multidisciplinary team of IP experts who will work with you to create the most comprehensive plan, tailoring advice to meet your product design requirements and your company’s specific commercial needs.
Here for You
Should any issues arise that challenge the registration of your designs or infringe your design patent, the Ehrlich Group has a hugely qualified team of experienced litigators with a successful track record of representing clients in all design related legal proceedings before the Patent Office and the courts, including appeals regarding the registration of designs, cancelation proceedings, unregistered design infringement, passing off, unjust enrichment, and more.
Feel free to speak with the experienced attorneys to help you protect your designs, as part of your overall intellectual property strategy.
Understandig Your Needs
A trademark identifies products or services. It can consist of letters, illustrations, or other graphic symbols such as the product name. Whatever the industry, when you think of some of the world’s most recognizable trademarks, they have a robust trademark strategy in place that distinguishes their brand, product, or service from others.
Registering a trademark is important because it ensures that no one else uses a trademark that is too similar to yours, but it isn’t enough to just register your trademark. It’s important to ensure that the underlying trademark strategy is sound.
Adding Value
With an extensive roster of global corporates and multinationals across all industries, the Ehrlich Group creates the comprehensive trademark strategy for you, tackling all aspects of trademark prosecution and enforcement, helping you to identify strong and valid trademarks, slogans and domain names, securing their clearance, completing the registration processes in Israel and abroad, and overcoming any potential opposition or cancellation proceedings.
Here for You
Should you face challenging situations of trademark infringement, passing off, unjust enrichment, or unfair competition cases, you draw on the vast experience of the Group’s litigators who have represented clients at all levels of the Court system and before the Israel Trademarks Office, and successfully resolved these disputes. We also lead the fight against counterfeit goods using your trademark, handle any competition procedures between trademark applications pending at the Israeli Trademarks Office, and support clients who are looking to license out or transfer their trademark.
As a valuable tool in your IP arsenal, whether you are looking to register, protect or enforce your trademark, get in touch and let us help you.
Understandig Your Needs
A trade secret will naturally vary from sector to sector and can include formulas, databases, methods, processes, business plans and much more. Trade secrets are the only type of IP – a “secret sauce” that must not be disclosed and are often considered to be a company’s most precious assets and key to the company’s success. Your start-up’s trade secrets are meant for you and a failure to protect them could have massive financial and legal consequences.
Adding Value
Working with the Ehrlich Group gives you both complete confidence and immediate access to experts who are highly skilled in identifying and distinguishing what needs to be protected as a trade secret, as a patent, or as a combination of both, in any industry.
Here for You
We work with our clients to develop the best possible protection strategy, from the time of identification of the trade secret to its incorporation into a client’s IP portfolio, through to ensuring maximum protection – when and if faced with third-party infringement. In this regard, our lawyers of Ehrlich, Neubauer & Melzer (EN&M) are solely focused on ensuring that any trade secrets violations will be swiftly and effectively managed.
If you have any queries about trade secrets, their value, or how to fully protect them, talk to our IP experts who can guide you.
Understandig Your Needs
Authors who create original works are legally granted the right to copyright their works, which have often cost them in many hours of work, sweat and tears. Today, copyright is an integral part of a company’s business model in many, many industries, including software, publishing, gaming, art, music, photography, architecture, television, and cinema.
Unlike trademarks, patents and design rights, copyright is an automatic international right. The copyright does not protect mere ideas but the specific form in which they are expressed. Our team of IP experts works closely with clients in Israel and abroad to register and protect their copyright, and as such, their competitive advantage.
Adding Value
With over 20 years’ experience, our Copyright team has a long and successful track record in helping businesses and individuals on a wide range of copyright issues, including licensing, transactions, enforcing their rights if a third party uses their works and infringe their rights.
Here for You
If you have questions about your copyright, please get in touch with one of our qualified lawyers of Ehrlich, Neubauer & Melzer (EN&M), part of our Ehrlich Group.
Understandig Your Needs
Plant breeder’s rights (also known as plant variety rights) are a form of intellectual property rights that grants breeders a monopoly over a new variety of plant. Registration and protection of plant breeder’s rights demands specific legal and technical knowledge and experience with regards to this complex field of intellectual property. Our team of IP experts specialize in handling every aspect of protecting our clients’ IP in plant variation, including registration, licensing, transactions and enforcement.
Adding Value
Our IP experts formulate a protection plan for our clients, handling all aspects of registration of the plant breeder’s rights in order to secure the widest protection available. Starting with a technical analysis and identification of new plant varieties, to drafting and filing the application. We also have close relationship with the Plant Breeders’ Rights Unit within the Ministry of Agriculture and Rural Development and in-depth knowledge of the agricultural and plant variety markets.
Here for You
Please feel free to contact us if you have any question about the services we provide regarding Plant breeder’s rights.
Understandig Your Needs
Patent term extension (PTE) allows the extension of the term of protection for a patent claiming a product that requires regulatory approval prior to being sold, under certain conditions. PTE aims to restore part of the patent term that was lost, while the patent holder is awaiting regulatory approval for the product. Such products include pharmaceuticals and medical devices under Israeli law.
However, the specific conditions and requirements for granting a term extension vary between jurisdictions. Our IP experts have vast experience in applying and obtaining PTE in Israel and in other applicable jurisdictions.
Adding Value
The process of obtaining PTE can be complex, as it is very detail oriented and requires specific knowledge and experience. It requires filing an application in this regard to the Patent Office or a motion to Court in each jurisdiction where PTE is available within a pre-determined period of time, in accordance with local procedure.
Here for You
Our experts are highly qualified patent attorneys and lawyers with vast experience in complex issues and processes regarding the pharmaceutical industry and hold a comprehensive understanding of the steps necessary to secure a patent term extension.
Please feel free to contact us if you have any question about the services we provide regarding patent term extension.
Understandig Your Needs
A due diligence process is a comprehensive legal investigation into a company’s financial and commercial capabilities and assets, including its IP portfolio. In most commercial transactions, especially in transactions involving technology, it is necessary to properly evaluate the associated opportunities and risks with regards to the relevant IP assets. Our IP experts at Ehrlich Group are experienced with performing in-depth due diligence in various complex transactions including mergers, acquisitions and joint ventures in every technological industry.
Adding Value
We conduct a thorough, in-depth IP due diligence process for our clients before closing transactions. This way, the company can get a clear and comprehensive view of the IP stand point in order to properly evaluate the transaction and take every measure to eliminate risks of litigation. With collaboration from the law firm Ehrlich, Neubauer & Melzer (EN&M) , we are able to properly address every single legal aspect surrounding the due diligence process for our clients.
Here for You
Ehrlich Group understands the need for highly qualified professionals with an advanced understanding of both the technical and legal issues involved in complex transactions. Our team of IP experts will make sure your company gets the most comprehensive due diligence and will guide you through the successful completion of your transaction.
Please feel free to contact us if you have any question about the services we provide regarding due diligence.
Understandig Your Needs
As one of the world’s leading innovation ecosystems, Israel, home to the largest number of start-ups per capita globally, as well as hundreds of R&D centres of some of the world’s largest multinationals and some of the most educated and ambitious inventors.
The vast majority of patent applications include inventions that were invented by an employee of the company. A ‘service invention’ is an invention made by an employee during the course of their employment and as a consequence of their professional duties. Within this landscape, inventors of cutting-edge products or services face many challenges regarding the ownership and compensation for such an invention. In recent years, there has been a significant rise in claims made by inventors, R&D companies and other parties.
Adding Value
Most of the time, these disputes include complex legal and technological matters. In these disputes, we have supported employees and employers in complex service invention disputes brought to Israeli Courts, the Israeli Patent Office and the Compensation and Royalties Committee.
Here for You
In close and seamless collaboration between the different arms of the Group we combine the patent attorneys’ understanding of the technical aspects of the inventions with the legal knowhow of the lawyers of Ehrlich, Neubauer and Meltzer (EN&M), to resolve service inventions disputes for those R&D companies, institutes and employers, as well as the inventors often working for them.
The growth of technological and scientific R&D entities in Israel has made service inventions one of the most important legal issues in Israeli patent law. Whether you are a concerned employer or an inventor, contact us with any question about service inventions and the relevant services we provide.
Understandig Your Needs
Between your day-to-day operations and a focus on growing the business, protecting intellectual property, innovation and brand reputation can sometimes be pushed to the backburner. With the value of your business often tied to its IP, we seize the initiative if your IP is threatened, commencing litigation if necessary and responding swiftly and decisively to keep your IP secure.
Adding Value
Regardless of size, clients are put at ease at the outset, reassured by the vast legal experience, multidisciplinary knowledge and enviable track record of our litigators who have successfully resolved the complete range of IP disputes. We tailor the solutions to address clients’ own particular business, scientific and technical issues and demands, according to the range of sectors in which they operate, from pharma to biotech, telecommunications to software, medical devices to consumer products, and many more.
Working closely, seamlessly and naturally with the rest of the Ehrlich Group, the lawyers of Ehrlich, Neubauer & Melzer (EN&M) advise on all manner of disputes, whether infringement of patents, copyright, trademarks, designs, trade secrets and all proceedings before the relevant Israeli courts and the Patent and Trademark office.
Here for You
Having been educated or worked abroad, notably the US and UK, our team works closely with other top tier law firms around the world, remaining actively involved in the technical aspects of any cases overseas. This allows us to offer litigation support services locally, thereby reducing litigation costs.
If you have an emerging dispute or are looking to avoid IP litigation from the start, contact the lawyers of Ehrlich, Neubauer & Melzer (EN&M), part of the Ehrlich Group, to find out how we can help.
Understandig Your Needs
An open source is a software whose source code is open and accessible to all. This allows anyone who wishes to do so to take part in the software development and contribute to its improvement. Nowadays, many technology companies use this kind of business model to encourages free collaboration. However, it can also present challenges and risks to the company, especially with regards to the company’s IP assets. Our IP experts have the most advanced technical and legal understanding to ensure our clients’ assets are properly protected while engaging in open source.
Adding Value
We build our clients a tailored strategy when handling their open source issues, and all other related computer law matters, including drafting patents for software based inventions; handling copyright matters in software; carrying out due diligence processes in transactions involving open source and other types of software; handling enforcement of IP rights in software, and drafting and negotiating various types of licenses, agreements and contracts, including, inter alia, user licenses, software development contracts, EULA and SaaS agreements, and many more.
Here for You
Our diverse team, including holders of M.A. and PhD degrees in software related fields and experts with vast practicing experience in these areas. With in-depth understanding of the technological developments in this rapidly changing industry, our firm is able to provide the most cutting-edge advice to its clients involved in open source software.
Please feel free to contact us if you have any question about the services we provide regarding open source.
Understandig Your Needs
Start-ups need to develop an intellectual property strategy in order to commercialize and monetize it. Commercialization of IP and technology is carried out through a wide range of agreements. Whether signing a licensing agreement, protecting the IP during the course of the business, or agreeing to sell the IP asset, you will need to carefully balance your priorities and objectives with the best possible IP agreement for your business.
These agreements frequently will have special characteristics, building a bridge between the IP at the heart of the transaction, and the contractual legal aspects, and, as such, they call for a significant level of legal, technological and scientific expertise.
Adding Value
Clients are immediately at an advantage by working with our hugely experienced lawyers who structure tailored and relevant IP agreements, licenses and commercial transactions that help them, as well as having access to our dedicated commercialization branch, IPTrade, which has developed a successful track record in monetizing IP. This includes negotiating commercialization transactions, such as licenses in all fields of science and technology, open-source licenses, IP Ownership agreements, R&D agreements, confidentiality (NDA) and Trade Secret Protection agreements, and much more.
Here for You
Drawing on our own scientific and technical backgrounds, our IP experts conduct a thorough due diligence procedure to give you a clear and comprehensive view of the intellectual property in question so that we can choose the best transactional route to go down, while taking all possible measures to avoid risks of future litigation.
Which intellectual property agreement is right for you? Do not hesitate to contact us with any questions.
Understandig Your Needs
Once identified and registered, protecting an intellectual property asset remains vital to a company’s ongoing success. When faced with the threat of, or actual litigation, or when initiating litigation is required, trusting experts is critical. With its successful track record both in Israel and abroad, the Ehrlich Group is here for you.
There is no substitute for experience and our clients rely heavily on our knowledge and skills when it comes to litigation and litigation support. If you are preparing for IP litigation abroad – whether patents, trademarks, trade secrets, unfair competition, and so on – we help you find the appropriate overseas counsel and remain actively involved in the technical aspects of your cases overseas, including those in US, Europe, the UK, Far East and in many other jurisdictions.
Adding Value
We frequently work on contentious matters relating to the U.S. that often refer to the filing and prosecution of patents there and are able to draw on the experience of our US patent attorneys in-house, as well as our skilled team of litigators, many having trained and worked in the U.S.
Wherever the jurisdiction, we represent clients and provide litigation support in matters relating to due diligence, the analysis of patents or patent portfolios during acquisition or investment, and in discussions with foreign patent holders who assert their patents against our clients.
Here for You
Our rich legal and academic experience, together with an unparalleled technical knowledge of many sectors, as well as concrete achievements in resolving IP litigation, help our clients to keep down the cost of litigation proceedings and leaves them feeling safe and reassured.
If you are facing an intellectual property dispute overseas, reach out and find out how we can help make this easier.
Understandig Your Needs
The race to success is more hurdles than sprint, and for start-ups, entrepreneurs and businesses, the best way to avoid regulatory setbacks and falls is to first understand relevant regulations and work to develop compliant policies and business practices from the outset.
For many years, the Ehrlich Group has thoroughly mapped out for clients their legal requirements, as well as the industry’s best practices to support their business strategies, ensure their compliance with all regulatory frameworks, and drive their success.
Adding Value
We specialize in marketing and advertising strategies that comply with regulatory standards in Israel and worldwide, closely monitoring developments in various industries. Our IP experts draw on a wealth of scientific and technological knowledge and a commercial perspective to support clients operating across many sectors, including highly regulated industries, such as pharmaceutical, medical devices, food supply and others.
Here for You
Speaking your language, we put this into business terms that can be swiftly and practically implemented, mitigating legal and business risks and giving you the freedom and confidence to do what you do best: Run your business.
Please feel free to contact us if you have any questions about regulation and compliance.
Understandig Your Needs
You create an incredible product and begin to make money. Soon, other companies catch on and some may try to profit from your ideas. With international counterfeiting and piracy on the rise, brand owners know they must be vigilant when it comes to dealing with counterfeit goods so that they can protect their own brand’s reputation and value. This is why the protection of your patents, copyrights, designs and trademarks are so important, right across every industry.
Adding Value
We have built up a longstanding and highly respected anti-counterfeiting and intellectual property enforcement practice, with the full arsenal of weapons to safeguard your brands. A prime destination for Fortune 500 brand owners and emerging companies, we take a proactive and hands-on approach, with a team of professionals building a comprehensive and effective strategy to protect brands, using all necessary enforcement methods to reduce piracy.
Here for You
With a successful track record in tackling, head-on, anti-counterfeiting litigation, our team has developed close working relations with the Israeli Police and the Israeli Customs Authorities, vital pillars of defense against counterfeit goods and piracy.
Please feel free to contact the lawyers in Ehrlich, Neubauer & Melzer (EN&M) of the Ehrlich Group, should you have a question about the services we provide regarding anti-counterfeiting.
Understandig Your Needs
Whether you are a high-tech company or a private owner of technology-related patents, IPTrade is Israel’s premium service for monetizing your intellectual properties on the global markets.
Tier-1 enterprises, start-ups and private inventors choose to partner with IPTrade, utilizing our vast expertise in order to leverage the untapped value of their intellectual property. From assessing a patent’s worth and sourcing it to prospective buyers, to maximizing its value and negotiating a sale, IPTrade works closely with many owners of technology-focused patents registered in the U.S. and elsewhere.
As a client of IPTrade, which is the most effective, successful and valued channel to monetize your IP on the international stage, you will also have access to the steadfast support of the Ehrlich Group. Through this unique collaboration, you will benefit from the first-class patent prosecution expertise of Ehrlich & Fenster and the comprehensive litigation experience of Ehrlich, Neubauer & Melzer. in addition to the monetization expertise of IPTrade.
Partner with the Ehrlich Group, where your ideas are valued.
Patent Sales
Once you are happy with the accurate valuation of your patent, we then strategize with you to source genuine prospective buyers, undertaking all necessary due diligence before presenting the IP assets to the buyer, negotiating the best possible price for you and arranging the contract documentation to swiftly complete the transaction and collect payment.
Whether you are selling your intellectual property for the first time or you are a seasoned veteran, you are reassuringly supported by the Ehrlich Group in its entirety, which together with IPTrade protects your patent from start to exit, monetizing your intellectual property on the global market for maximum return.
Concept
Many registered inventions will ultimately fade into obscurity, their value left unexploited due to meager financial resources, limited entrepreneurial skills, inconvenient market conditions and other factors.
Often, the best way to maximize the value of patents whose commercial realization remains undeveloped is to simply sell them to a third party for whom they have strategic importance. Once the sold patents become part of a wider IP portfolio, owned by an established hi-tech corporation, they transform into powerful assets, which can often improve the competitive standing of that company in its respective market.
But what chance does a small or medium sized start-up have, to successfully and profitably sell its patent to the highest bidder?
With IPTrade as your partner we can make that happen. On behalf of our talented inventor clients, IPTrade is committed to exposing Israel’s vast reservoir of technology-based intellectual property to the world.
Team
Our Team

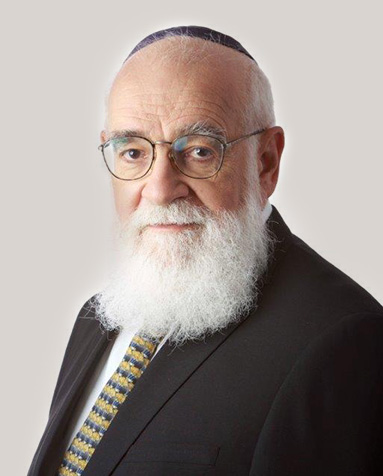
Dr. Gal Ehrlich
Founder and Managing Director
Dr. Paul Fenster
Head of Local and Foreign Litigation Support B.E.E., Ph.D. Electrophysics
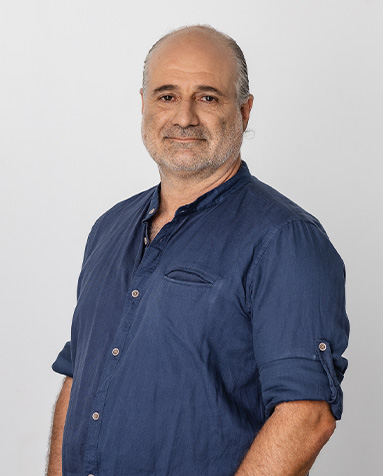
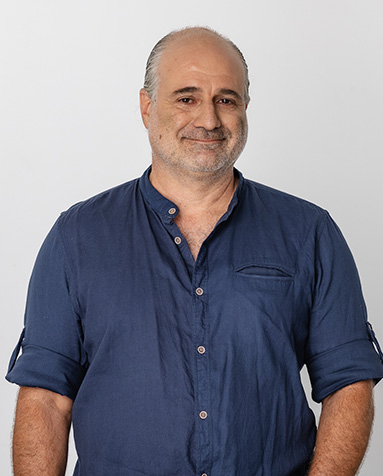
Maier Fenster
Head of Medical Devices Department
Amit Ehrlich
Vice President, Legal Counsel
Roy Melzer
Head of Computing Technologies
Dr. Hadassa Waterman
Head of Biotech Department
Dr. Revital Green
Head of the Pharma&Chemistry Department
Geoffrey L. Melnick
Head of Hitech
Dr. Eran Naftali
Head of Physics Department
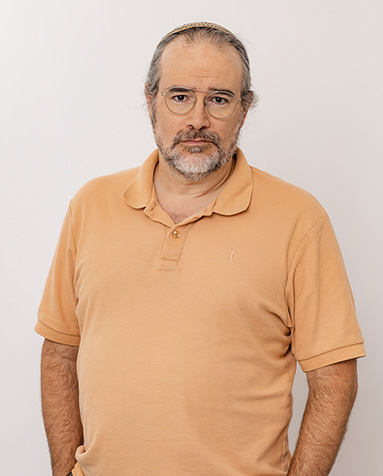
Yehuda Neubauer
Head of IP Litigation, Head of Trademarks and Design Department, LL.B., LL.M
Recognitions
Award winning firm







Chambers
Prestigious ranking guide, Chambers Global, has recognized Ehrlich Group as a Band 1 firm in IP Prosecution, with four ranked individuals (more than any other law firm in Israel) - Band 1 Gal Ehrlich and Maier Fenster along with Roy Melzer and recently added Hadassa Waterman. In addition, Yehuda Neubauer was recognized among the leading individuals in IP.
According to Chambers, "Ehrlich Group is a first-rate law firm with a strong reputation," with clients calling "the team both technically strong and legally proficient."
Chambers Global ranks the top lawyers in over 200 jurisdictions. A very well-respected directory, Chambers claims that their legal rankings are the most thorough and well-respected in the market.
Duns100
Ehrlich Group is one of three firms listed as top-tier in patent and prosecution in Israel and ranked among the leading firms in IP litigation by the domestic Israeli ranking guide Duns 100.
The Duns100 rankings present the leading companies in a range of economic sectors and reflect Israel's business reality in a reliable, accurate, and professional way.
BDi CODE
Ehrlich, Neubauer & Melzer Attorneys at Law of the Ehrlich Group have been ranked top-tier IP firms by the domestic Israeli ranking guide BDI Code. In addition, the guide ranks the firm among the leading Patent Attorney firms in Israel. CofaceBdi is Israel's largest business information group, with information on 30 million companies and businesses worldwide.
IAM Strategy 300 Global Leaders
Ehrlich Group has four lawyers listed as Global Leaders by IAM Strategy 300. This is more than any other firm in Israel. "A slot in the 300 is the mark of a professional whose approach to intellectual property is regarded by peers as truly strategic in nature." Gal Ehrlich, Roy S Melzer, Yehuda Neubauer, and Hadassa Waterman have reached this accolade.
As the go-to resource in listing first-class IP strategists, IAM Strategy 300 focuses exclusively on patent practitioners identified through confidential nominations.
iam Media
Ehrlich & Fenster ranked Tier 1 in Patent filing & prosecution “Clients say that they enjoy cooperation with ‘very good patent attorneys in different technological fields’ at Ehrlich & Fenster.”“Attorneys at the firm draft applications to provide meaningful protection for our business. They are familiar with the laws of the main jurisdictions and take them into account.
They have very good administration, which is important for patents. “It is considered to be one of the best patent prosecution firms in Israel. Gal Ehrlich, ranked as a Patent Star, is highlighted for his services in patent law, noting that, Gal Ehrlich combines thorough understanding of a client’s business needs and the ability to expose the heart of an invention in its broader scope”.
Also noted as a Patent Star, “Hadassa Waterman is extremely smart and has the ability to see the big picture of the case. She can plan a strategy that will result in obtaining full protection for aspects of the invention, inline with the business strategy. Roy Melzer is also very good and combines creativity and practicality in drafting and prosecuting complicated cases”.
IP Starts
Ehrlich Group has been recognized as a top-tier firm in patent prosecution and among the leading law firms in trademark prosecution. Furthermore, Gal Ehrlich and Hadassa Waterman have been identified in the individual rankings as Patent Stars, with the latter being named a Top 250 Women in IP for 2023.
IP STARS is the leading specialist guide to IP law firms and practitioners worldwide. The research analysts evaluate firms for contentious and non-contentious work in several copyright-based industries, including software and entertainment, across jurisdictions.
WTR1000
Ranked among the leading law firms in Enforcement and Litigation, Prosecution and strategy, and IP transactions. According to WTR, Ehrlich Group's strength is demonstrated by its "stellar client base," which includes Bruno Mars, Huawei Technologies, and TikTok, to name a few.
Yehuda Neubauer, "a fast thinker and has exceptional personal and professional skills," Hilla Diller as "highly responsive and a great communicator," and Chamutal Niran, "an exceptional litigator [who] is instrumental in the work for Bacardi and Nintendo," are all recommended individuals by WTR.
The Legal 500
Ehrlich Group is ranked in the prestigious ranking guide, Legal 500, as a leading law firm in "Filing and Prosecution: Patents." And among the leading firms in Filing and Prosecution: Trademarks and Copyrights, as well as IP disputes. As quoted," Ehrlich Group is an IP boutique firm which is 'practical and technically knowledgeable,' drawing upon the expertise of legal and scientific professionals to deliver tailored advice to Israeli and international clients."
Gal Ehrlich has been recognized among the four leading individuals in Israel in IP fillings and prosecution: patents. Quoted by a client as having a "team of experienced and highly skilled attorneys," Maier Fenster, Roy Melzer, and Hadassa Waterman are recommended by the Legal 500.